THMHxSFDC SEPT CTF
Overview
OLDCTF
Challenges Solved
Kitchen Note
Challenge Description
While setting up the online restaurant portal, the Chef left behind a note tucked away in the system logs. It was just a half-written reminder about an old pantry folder, never meant for diners to notice. Anyone curious enough to peek might find the first clue hidden there.
Solution
Accessing the Target Site
Opened the Target site. Landed on a login page, but no credentials were provided.
Creating a New Account
Clicked the Sign Up option to register a new account. Filled in the required details and successfully created an account.
Inspecting the Page
Logged in with the newly created account. Opened the browser developer console (F12) to inspect scripts and logs. And there it was, printed in the console.
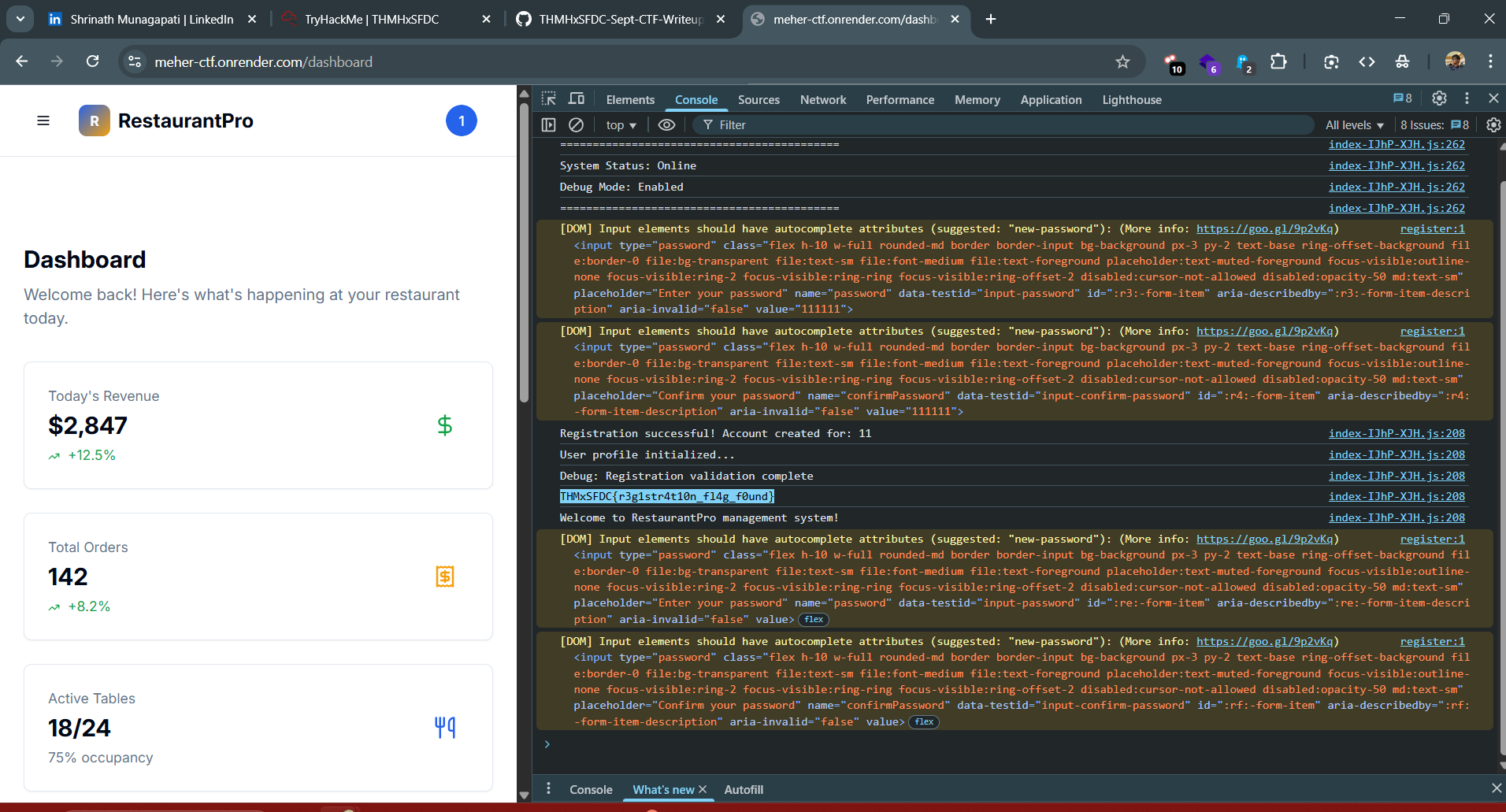
Flag
THMxSFDC{r3g1str4t10n_fl4g_f0und}
Forbidden Pantry
Challenge Description
The janitor once stumbled across the Chef’s private recipe book while navigating the staff portal. Not knowing its value, he marked the folder as restricted in the system’s back-end. That careless note still lingers, quietly hinting toward a forgotten archive.
Solution
Understanding the Story Clues
The story mentioned a “restricted folder” and a forgotten archive. This hinted that the content might be hidden but still accessible somehow.
Checking Site Metadata
Remembered that some hidden paths are often listed in robots.txt. Opened /robots.txt and found the flag waiting there.
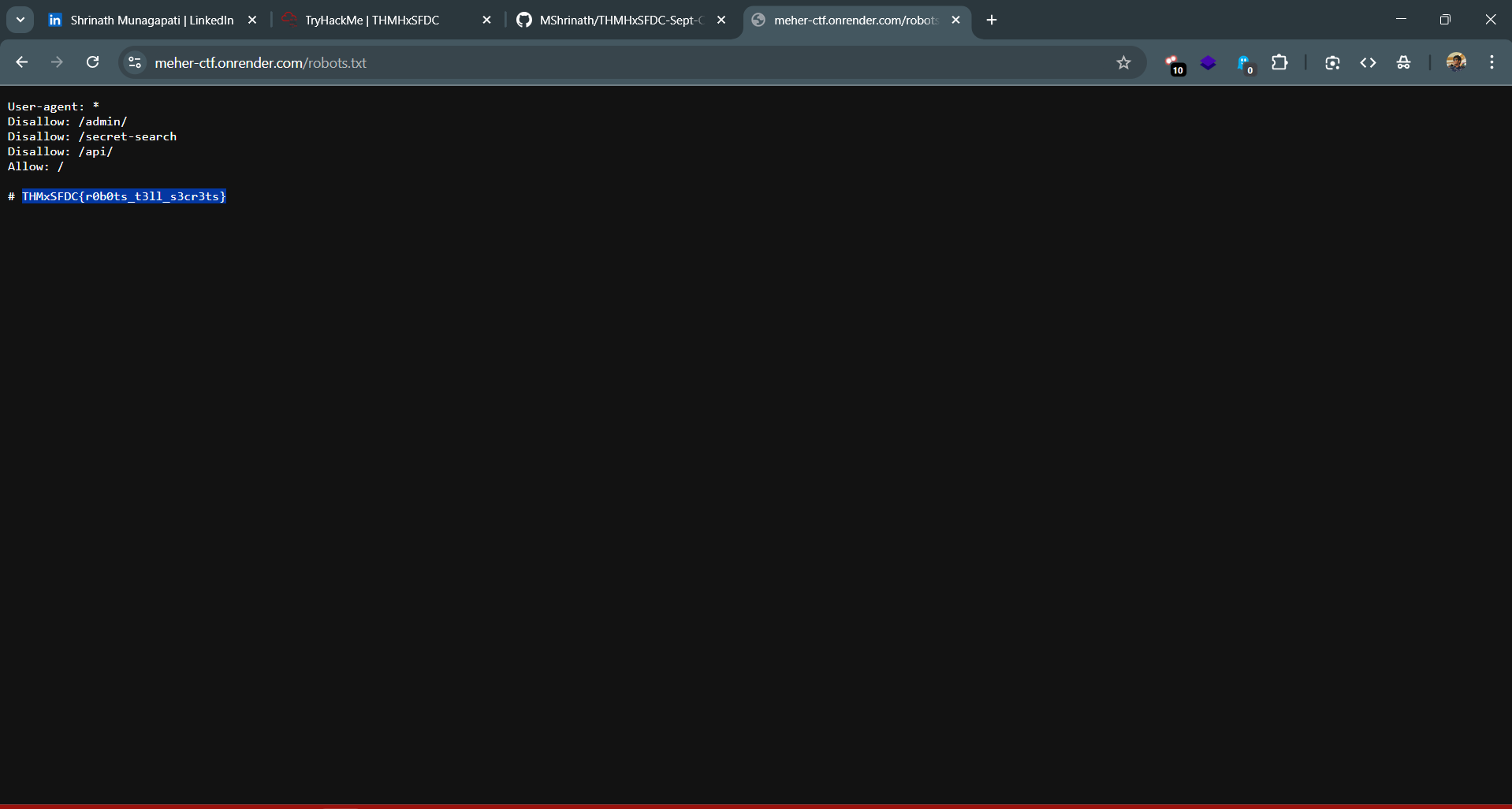
Flag
THMxSFDC{r0b0ts_t3ll_s3cr3ts}
Archivist’s Ledger
Challenge Description
Buried deep within the portal is the Archivist’s ledger, a digital record of recipes and notes that staff thought were long forgotten. It was meant only for the Chef and his closest aides. Yet the ledger is not guarded carefully. With the right kind of request, it reveals more than it should, including another fragment of the Chef’s secret book.
Solution
Observing the Story Clues
The story mentions a portal that holds the Archivist’s ledger. This hinted at a hidden interface or section in the site.
Exploring Known Paths
As seen in the previous subtask, the robots.txt file listed hidden paths. Noticed a /secret-search path which led to a Database Query Interface.
Testing for SQL Injection
Tried basic SQL injection payloads to see if queries could be manipulated. Successfully used 1 OR 1=1 and retrieved the contents of the ledger, which contained the flag.
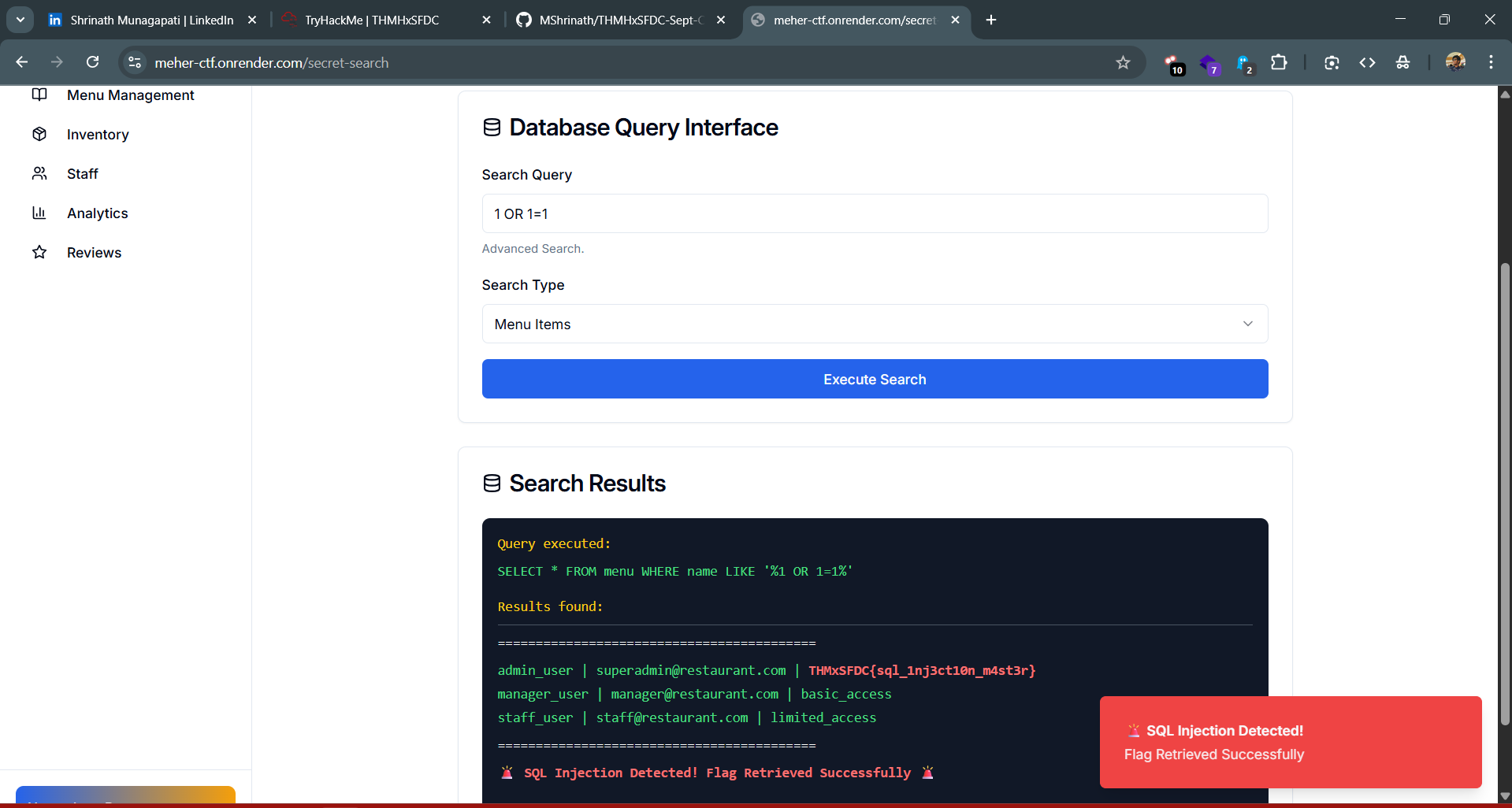
Flag
THMxSFDC{sql_1nj3ct10n_m4st3r}
Reflections of the Crowd
Challenge Description
Secrets do not always hide in logs and ledgers. Sometimes they slip through the voices of customers. The portal proudly echoes whatever is spoken, yet it does so without care. Clever diners have noticed that when reflections are repeated without question, even a casual remark can twist into something dangerous. In that distortion, another secret of Chef’s book is exposed.
Solution
Following the Story Clues
The story talks about the “voice of customers” and echoes, hinting at user-submitted content. Checked the dashboard, found a reviews page where diners could submit input.
Testing for XSS
The input was not sanitized, so tried a simple XSS payload:
<script>alert(1)</script>
It successfully executed, confirming a Reflected XSS vulnerability. The page revealed the flag in the process.
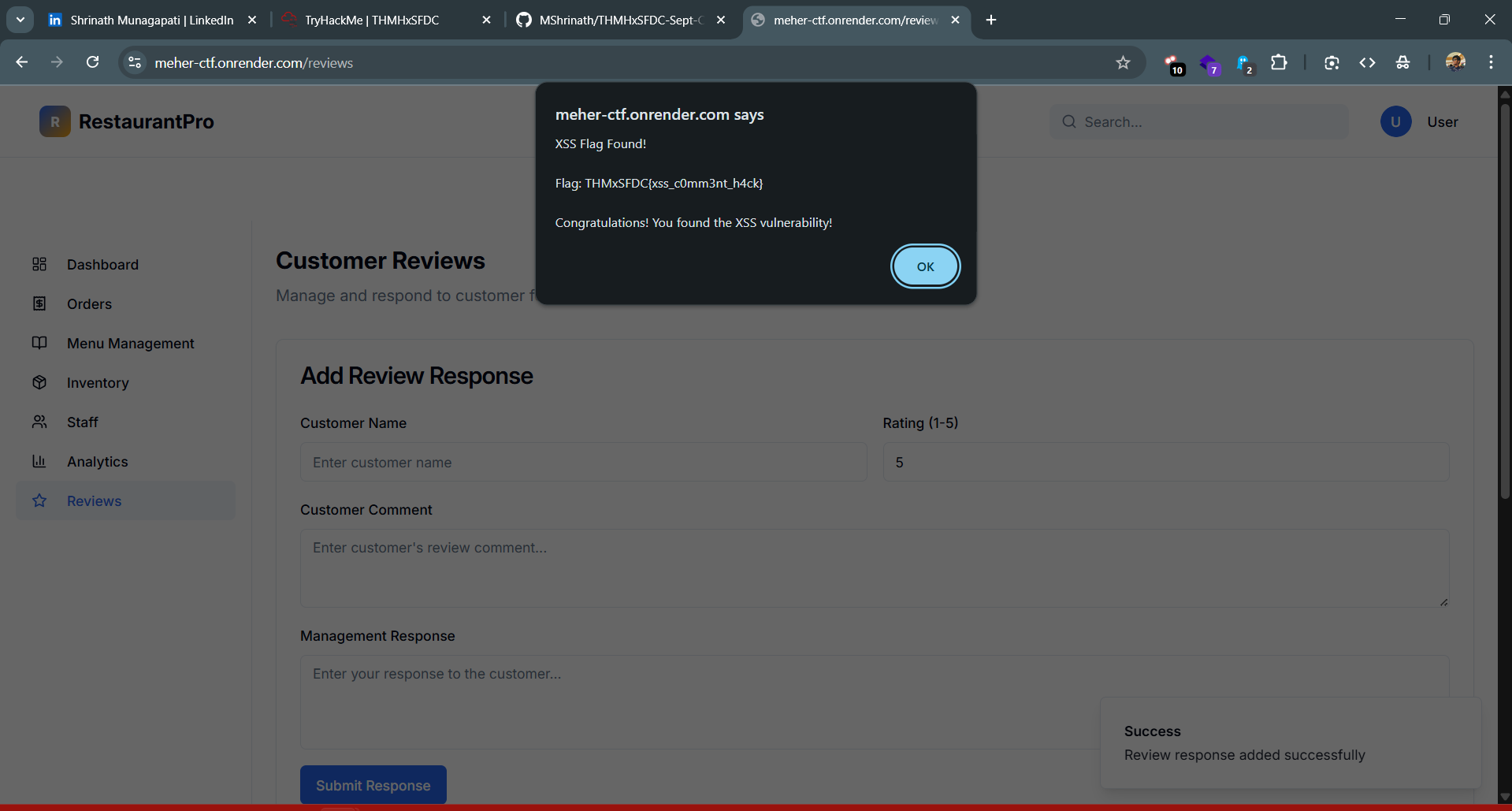
Flag
THMxSFDC{xss_c0mm3nt_h4ck}
The Hidden Pantry Ledger
Challenge Description
Behind the scenes of the portal lies a private ledger, a section meant only for trusted staff accounts. The locks on its digital shelves are weaker than they appear. A determined user who tampers with the right identifier can bypass the restriction and stumble upon records that were never meant for their eyes. Hidden among them lies yet another piece of the Chef’s secret book.
Solution
Following the Story Clues
The story mentioned a “private ledger” for trusted staff accounts, hinting at an admin-only section. Checked robots.txt and noticed a /admin path, likely where the private records are hidden.
Exploring the Admin Panel
Navigated to /admin and found a panel listing all users. Opened the network tab and saw an API call: /api/users Returning a JSON of all users, their IDs, and admin status — exactly the information the story hinted we could uncover.
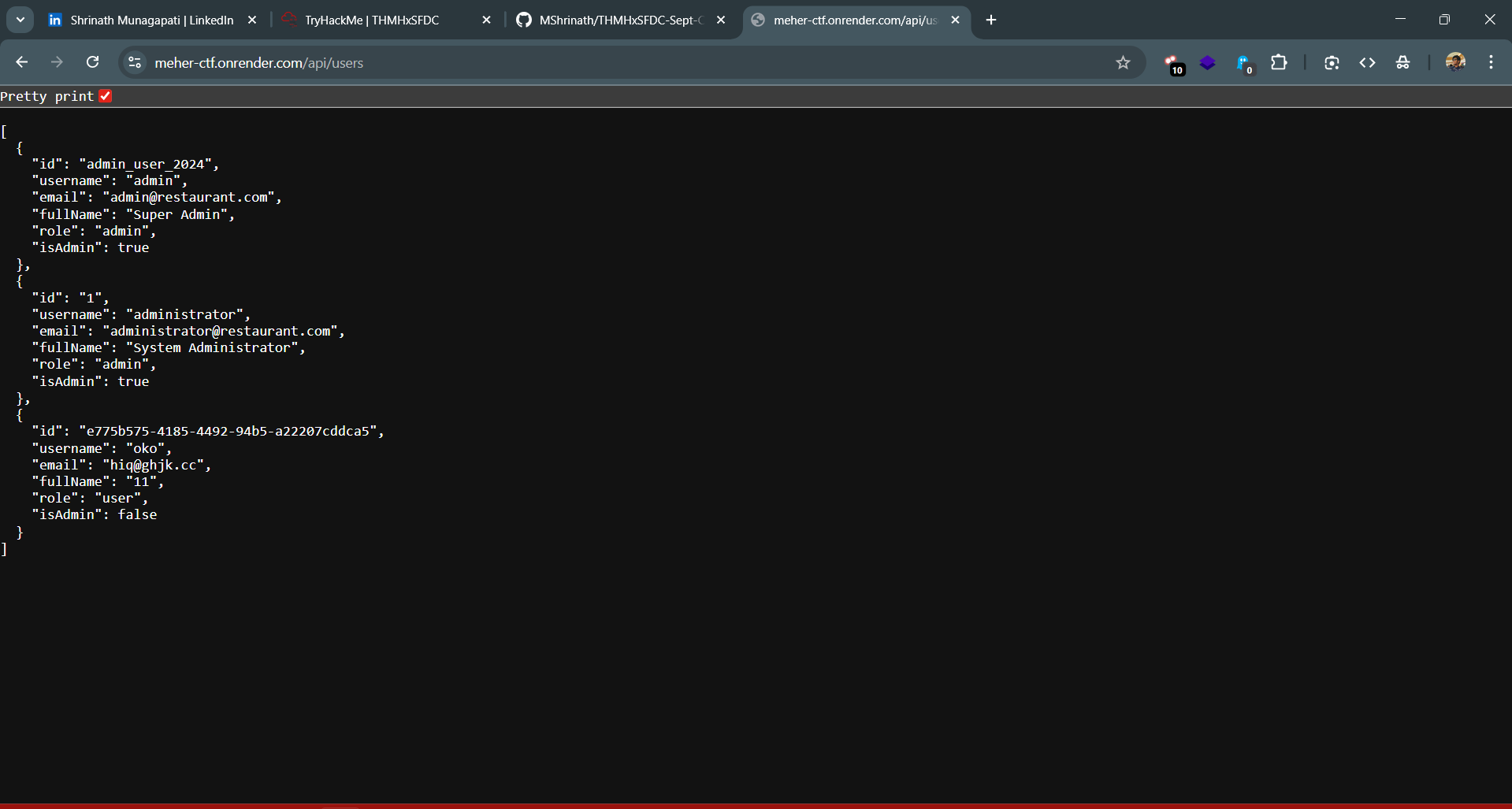
Accessing the Ledger
From the JS source code, found an endpoint: /api/user/profile/{id} Each ID needed to be Base64 encoded. Tried the IDs from /api/users after encoding them, and the API returned the corresponding user details.
Finding the Flag
Among the returned user data there was the flag, completing the final piece of the Chef’s secret book.
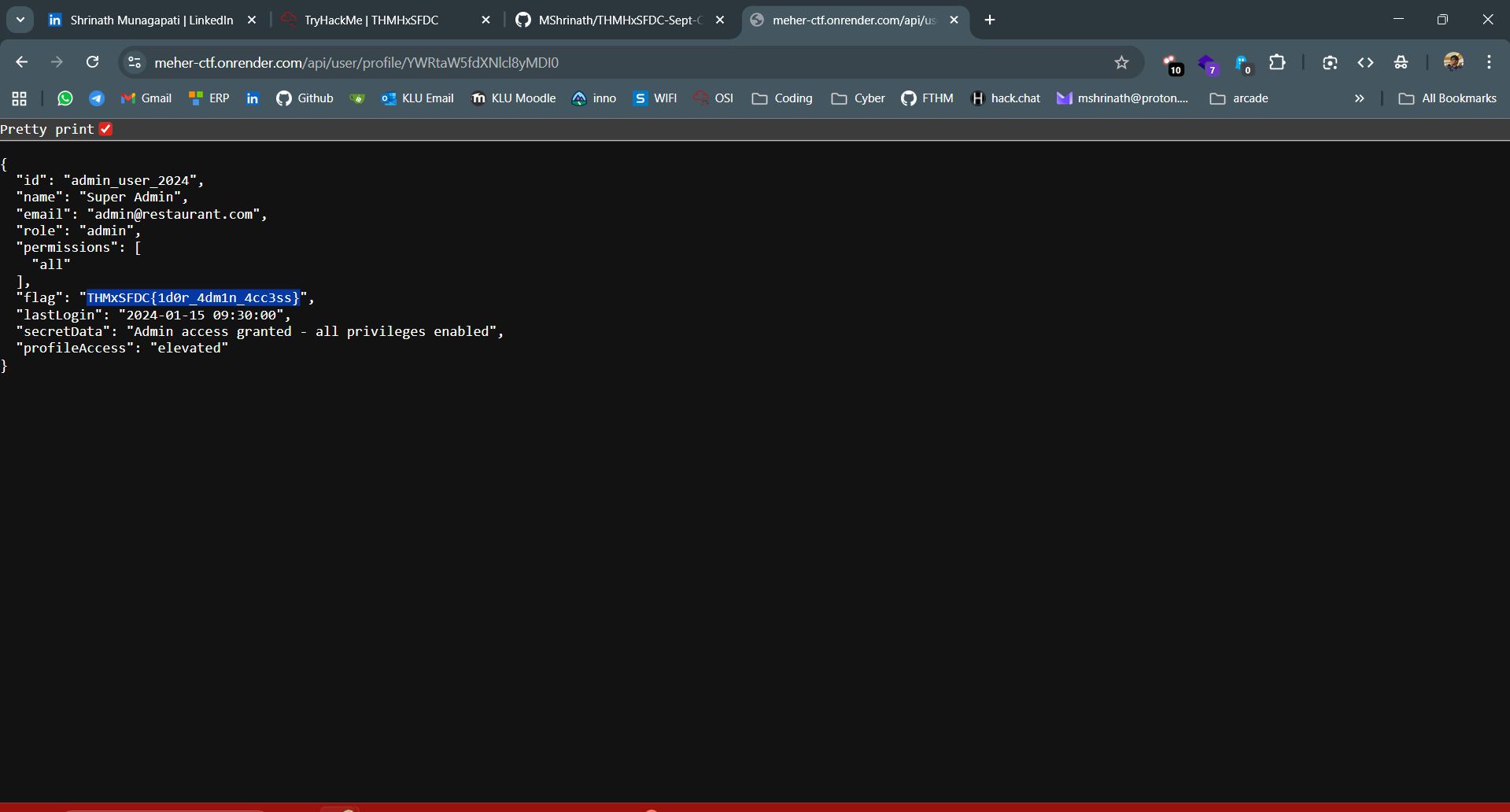
Flag
THMxSFDC{1d0r_4dm1n_4cc3ss}
Hospital Outbreak
Challenge Description
Analyse the logs (.csv) and answer the question. Which threat actor was responsible for this incident?
Solution
Initial Exploration
Opened the CSV in a spreadsheet editor. Examined the columns and rows to understand the types of events recorded.
Focusing on Suspicious Events
Filtered the event_type column for file_create events. Noticed multiple files being created with the .wncry extension.
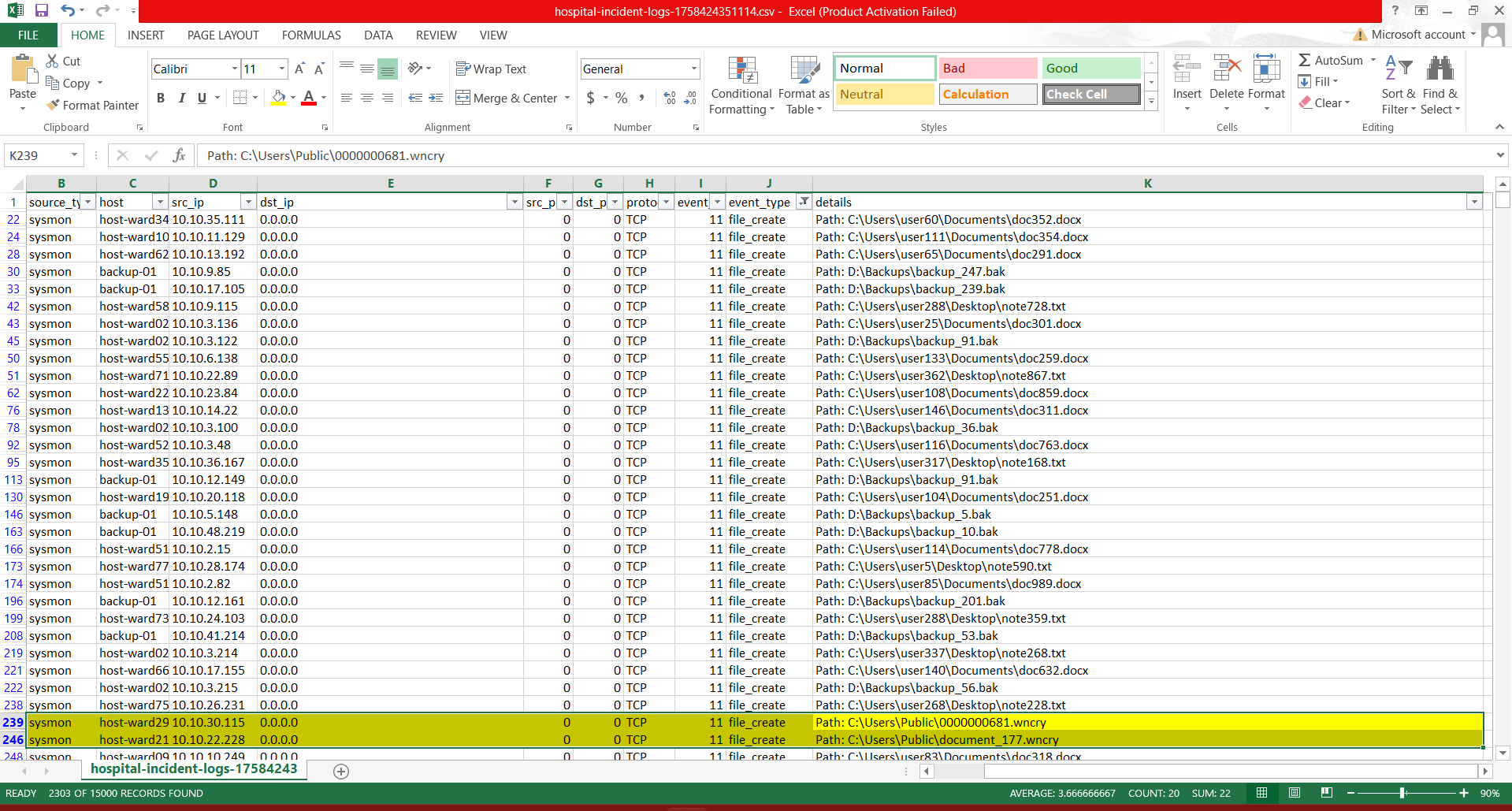
Connecting the Dots
.wncry is a known indicator of WannaCry ransomware. Quick research confirmed that WannaCry is attributed to the threat actor Lazarus.
Flag
lazarus
Silent Fetch
Challenge Description
Analyse the (.pcap) and answer the question. Which threat actor was responsible for the activity observed in the provided PCAP?
Solution
Initial Exploration
Opened the PCAP file in Wireshark. Browsed through HTTP and DNS traffic to identify unusual requests.
Identifying Suspicious Traffic
Found repeated attempts to access a domain: mustache.webstory.sa The traffic showed requests to /wp-admin, which looked suspicious.
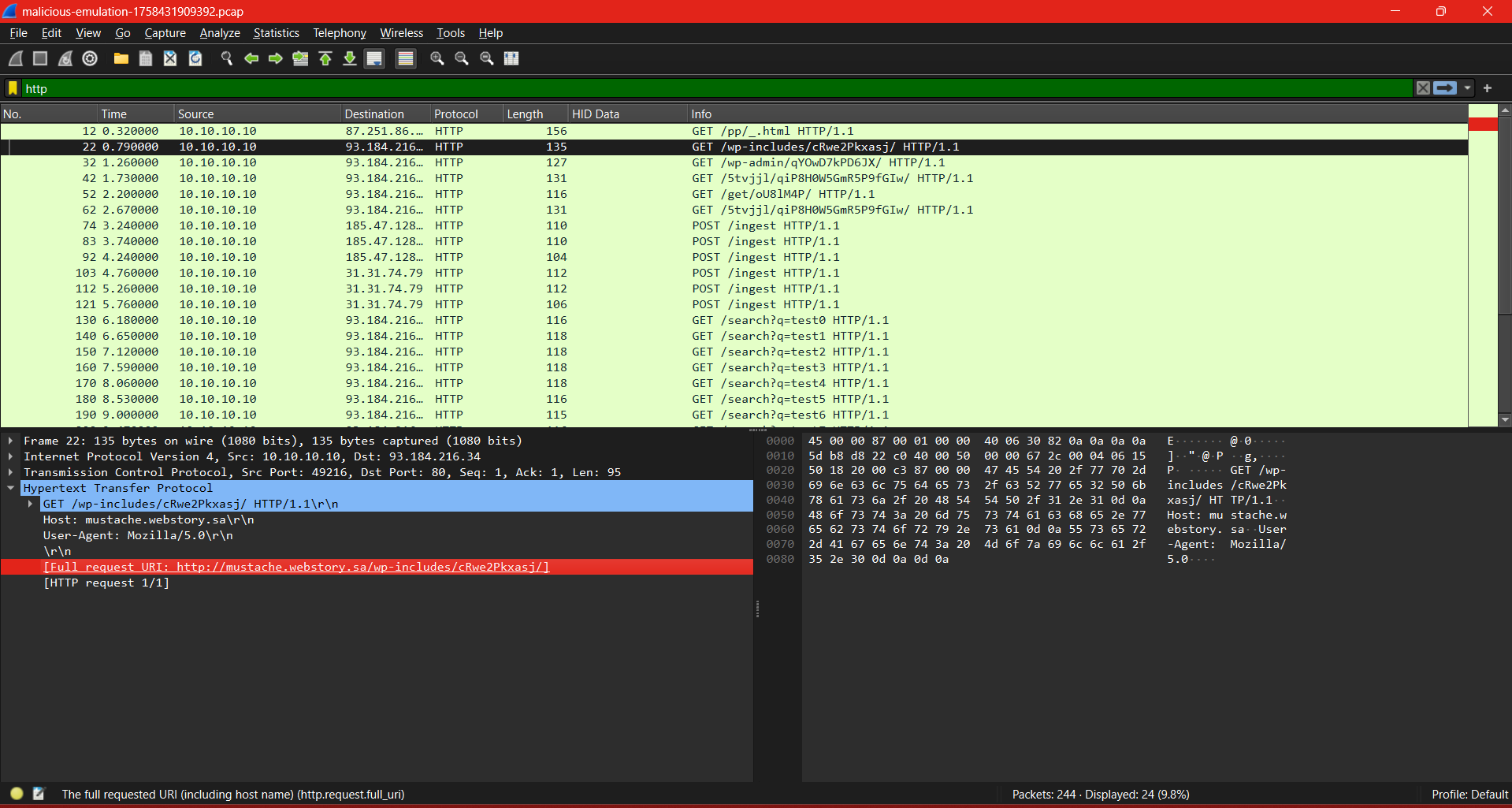
Domain Investigation
Tried to access the domain in a browser, but it was inactive. Performed an open-source search for mustache.webstory.sa.
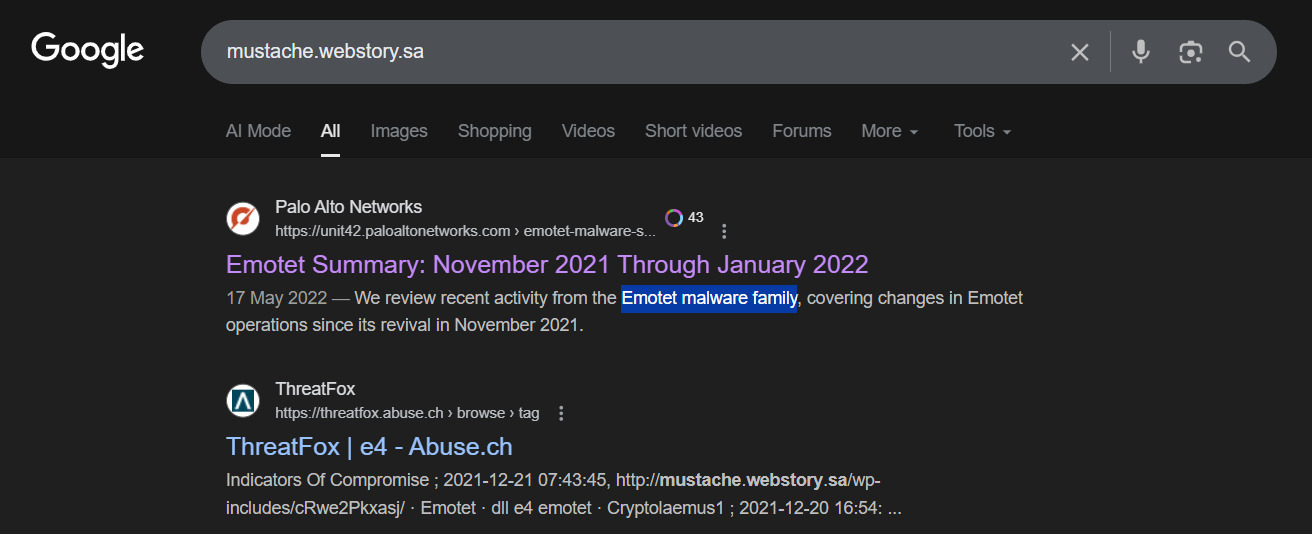
Threat Intelligence Correlation
Found threat intel reports and documentaries linking this domain to Emotet malware campaigns. Concluded that the activity in the PCAP was related to the Emotet threat actor.
Flag
emotet